Hi, picking up this old thread, could you please expand on this? For example how would one achieve this for the other plugins, to ensure that uploaded results are consolidated into the node of my choosing, pre-populated with hosts? I’d like to do this for all plugins I use, including nmap, metasploit, nikto, openvas and burp…?
Hi @Kalaratri,
Can you try the following?
- Create a top-level Node in your project called
plugin.output - Add some subnodes to the
plugin.outputNode and associate some findings with them. Make sure that these subnodes have the same name as the hosts in your scan(s) - Upload scan data! When/if the Node already exist under the
plugin.outputNode, Dradis will automatically add the new findings to that existing Node, it won’t create a new one.
So, if you already manually added subnode 10.0.0.1 under plugin.output, when you upload a Nessus file that contains a vulnerabilty that affects 10.0.0.1, it will be added to that existing subnode in your project.
Does this make sense? I’d encourage you to play around with the different options a bit to see how Dradis is currently dealing with different file types and combining them in your project. Any questions? Just let us know!
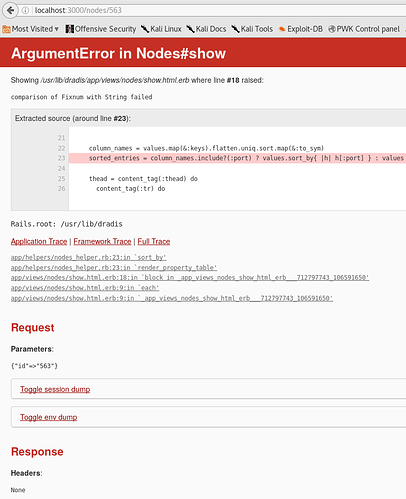
Hi Rachel, yes i tried that earlier today, albeit a slight variant, but ended up with the an error as attached and the results were not consolidated
I uploaded a small nmap scan that resulted in three hosts under plugin.output.
I then uploaded a larger metasploit db_export hosts database. This time it didn’t create a new plugin.output folder, but recreated (duplicated) the hosts under the same plugin.output node. When I tried selecting any of the original 3 nmap hosts I received the attached error. All of the Metasploit hosts work fine.
When using this approach, or keeping all tool imports under the renamed plugin.outlet nodes, there are multiple nodes of the same name, even under different nodes and these are duplicated in the HTML OSCP 0.3 template.
They were both identically named, e.g. 10.11.1.5
The workflow i’m settling on is pretty much using metasploit to consolidate all my nmap and nikto scans and then uploading the metasploit hosts database.
I also tried to change the parent node in the files below, to match my existing “Lab Network” node, but after restarting all services it still recreated a new plugin.outlook node
/usr/lib/dradis/app/models/configuration.rb
/opt/dradis-ce/app/models/configuration.rb
If there’s a more obvious way of achieving the aim of consolidating scan results from numerous tools under a single host then I’m all ears!
Thanks again for such a prompt reply!
@Kalaratri thanks for passing this on! I was able to replicate the same issue by uploading an Nmap file, then a Metasploit file that contained the same hosts. This actually appears to be a bug caused by the Services tables from Nmap and Metasploit not playing nicely together. I’ve passed this off to the technical team for further investigation and will let you know as soon as we have more details for you.
The good news is that Dradis is consolidating the scans as expected, we’re just running into this problem when displaying the Node due to the combined Services tables.
As a workaround in the meantime, would it work to patch either Metasploit or Nmap so that only one of them creates the Services table on the host? That should get things back to normal and avoid this error until we can get a fix for it. Just let me know which add-on (Metasploit or Nmap) you’d like to create the Services table from and I’ll send you details on how to comment out this action on the other add-on.
@Kalaratri there was a bug in dradis-metasploit that saved the port information as strings instead of numbers (!). If you navigate to that same page and append “/edit” to the end, you can tweak the JSON data from:
{
"protocol": "tcp",
"port": "445",
"state": "open",
"info": "Windows XP SP3 (language:English) (name:MAS) (domain:IA)",
"name": "smb"
}
to
{
"protocol": "tcp",
"port": 445,
"state": "open",
"info": "Windows XP SP3 (language:English) (name:MAS) (domain:IA)",
"name": "smb"
}
That being said, the bug is now fixed, if you git pull and bundle update dradis-metasploit you should no longer experience this problem.
Let us know how it goes!
HTH,
Daniel